ISO 27001 – A practical path for leaders who want more than a certificate
Most ISO 27001 projects stop at “pass the audit.” That’s fine when the only goal is a certificate. However, this approach leaves a lot of
Most ISO 27001 projects stop at “pass the audit.” That’s fine when the only goal is a certificate. However, this approach leaves a lot of

APIs are the backbone of modern businesses, facilitating seamless data exchange between applications, customers, and partners. But just like an airport without security checkpoints, unprotected
In the digital age, businesses rely heavily on their networks to function efficiently. However, managing and maintaining a complex network can be a daunting task. By implementing effective network management best practices, organizations can ensure optimal performance, enhance security, and minimize downtime.

In the ever-evolving landscape of cybersecurity, staying ahead of sophisticated threats demands innovative solutions. One such game-changer is NetFlow, a technology that unlocks a treasure trove of network traffic data. By leveraging NetFlow, organizations gain the upper hand in safeguarding their networks and detecting potential threats.
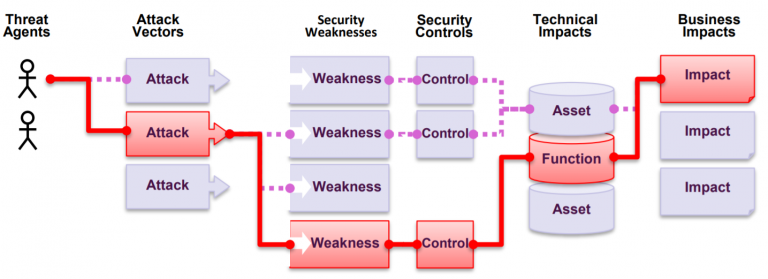
Splunk vulnerability analysis – CVE-2024-29946 & CVE-2024-29945 in relation to a common threat model. DISCLAIMER – The author of this blog shall not be held responsible for any negative outcomes that may occur as a result of following advice given in this blog. Caveat emptor – use advice and ideas presented in this blog at your own risk.

This is a case-study about the certification path of kicker.cloud, a very small startup company, its SaaS product and high ambitions aiming towards a global market. kicker.cloud encountered the same issues so many others have faced before and will in the future – the dreaded procurement Excel-sheets with seemingly endless amounts of security requirements that need to be addressed before any business deals can go ahead.
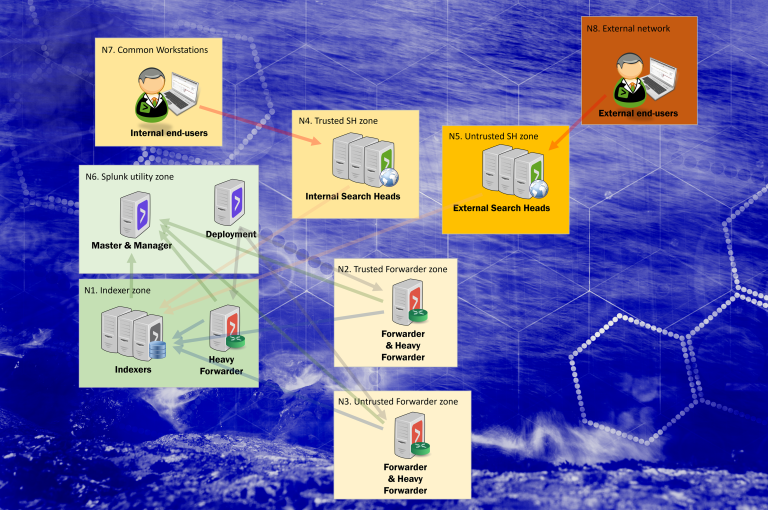
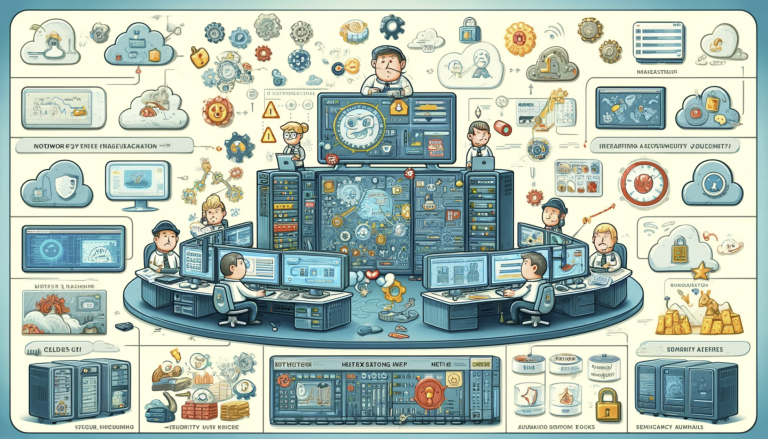
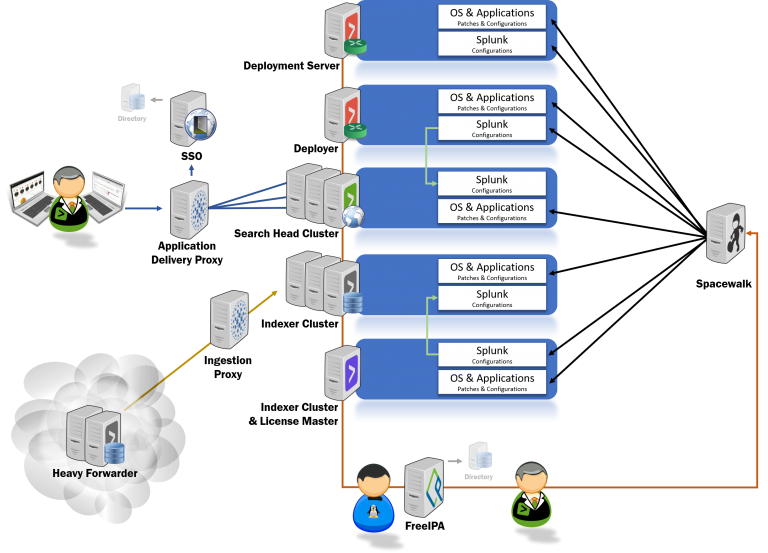
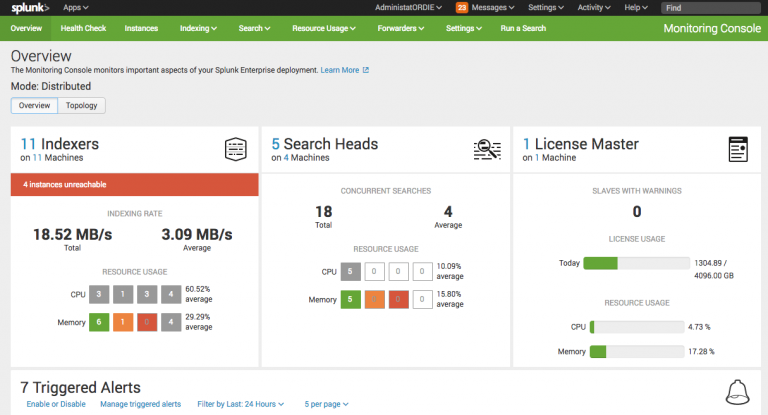
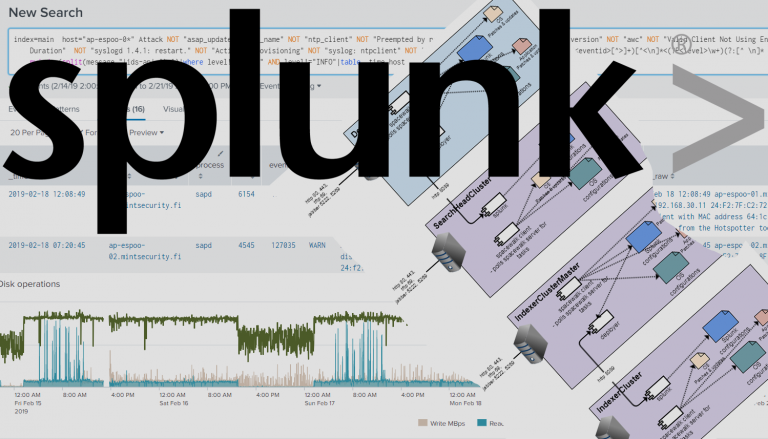
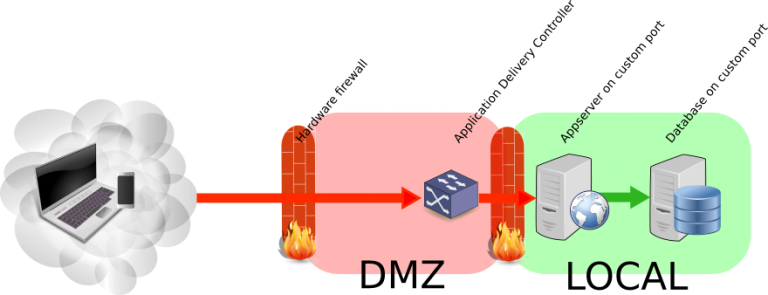
Splunk Enterprise (on-premises) can be setup in a vast number of ways, including hardening through network segregation. Splunk components chosen in the diagram are there to highlight where and why trust boundaries may or should be implemented.
Yhä useampi standardi, viitekehys ja asiakasvaatimus edellyttää – peräti huutaa – kirjastonhallinnan perään. Huutaa siksi että modernit sovelluskehitysmenetelmät ovat täysin riippuvaisia ulkoisista kirjastoista eli riippuvuuksista.

Within the context of ISO 27001, risk comes up as a topic all over the place. The standard itself, as most of ISO standards nowadays

As part of the ISO/IEC 27001 certification process, organizations must conduct regular internal audits to ensure compliance and identify areas for improvement. One common dilemma faced by businesses is whether to conduct these audits internally or engage an external company to do it.
The need for a cyber resilience exercise often starts from interest to gain verified information what each component is capable of — the capabilities, thresholds and baselines of the packet scrubber and other controls. Also, there is a need for training for crisis situations for organizations, as the threats for cyber resilience are on the rise.

Cloud Scanning -toiminto on Holm Securityn haavoittuvuuksienhallinnan uusi ominaisuus, joka automatisoi riskien tunnistamisen pilvi-infrastruktuureissa. Uusi toiminto kattaa Infrastructure as a Service (IaaS), Software as a Service (SaaS) ja Platform as a Service (PaaS) -palvelumallit.
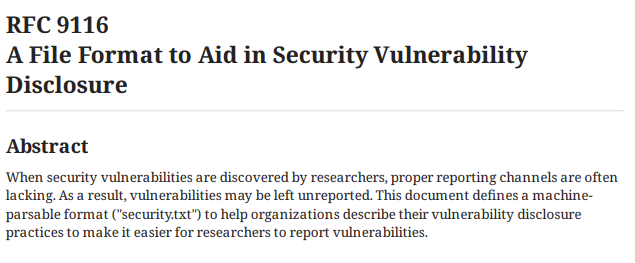
Having a security.txt in the root (/) folder of your website has long been a good practice. The contents of the file has been very free. What started out as a novel and great idea, is now an RFC. Let’s look a bit closer.

The first tasks of vCISO are usually to map the company’s real security needs, get to know the company and its business. A vision of obvious threats and threat models will emerge very quickly, for which rapid solutions can be found through an analytical approach.

Segregation of duties in ISO 27001 refers to all practices where information and/or privileges required to carry out a certain process are broken into fragments. The fragments are then distributed among multiple persons or roles in such a way that a single person alone cannot perform or fully control that particular process.
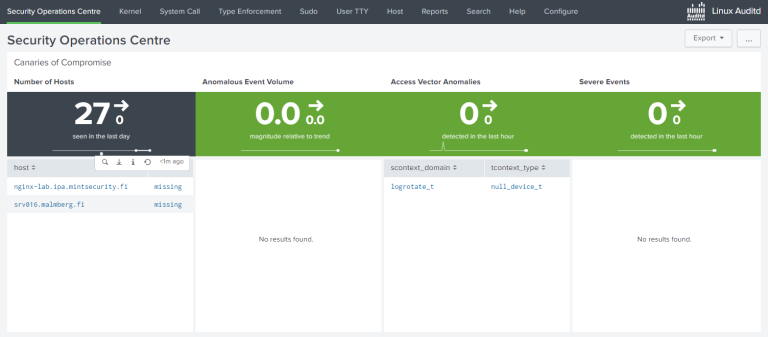
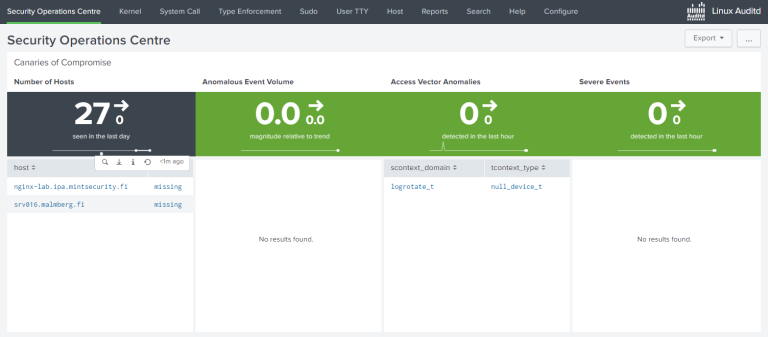
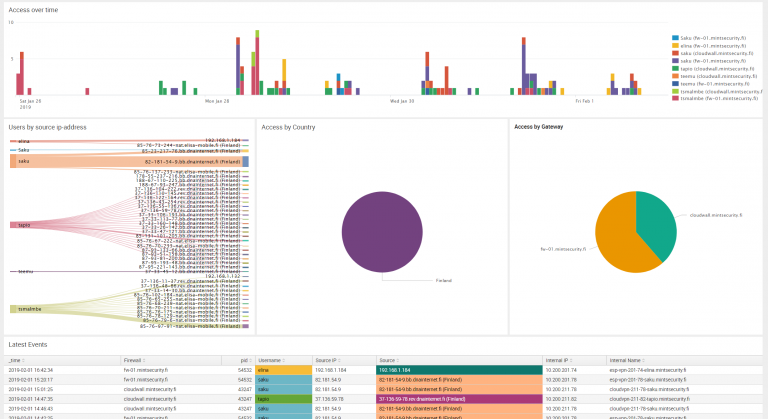
This is a follow-up to my previous blog on Auditd and Splunk. That one was about Defender ATP and Proxmox and license consumption. I did not really touch the subject of a good Auditd baseline configuration.
Similar to last year, we looked at the entire history of active applications, not just the activity associated with the application over one year. By doing so, we can view the full life cycle of applications, which results in more accurate metrics and observations.
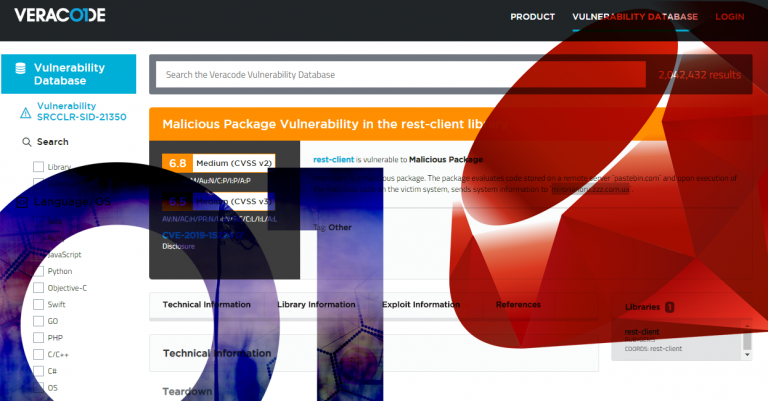
While docs.veracode.com (formerly known as help.veracode.com) is an excellent resource, it is not the most obviously intuitive tool out there. There’s got to be a
The average life expectancy of an ISO standard is about five years, at a time. When the hourglass has run out of sand, a voting will take place to decide whether to maintain the ISO standard as-is, revise it or withdraw the standard altogether.
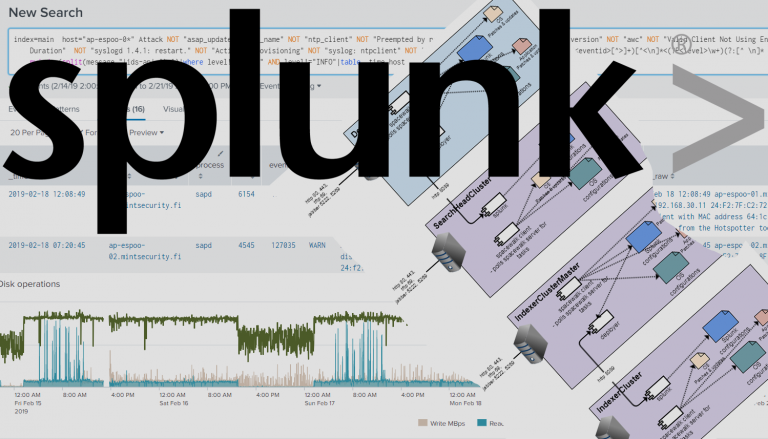
This blog post offers a few simple tricks and tips that will ensure that your security controls do not interfere with each other. The tricks are not really tricks, just plain old configurations which offers food for thought. As we know, Splunk is the most complex beast of a software out there.
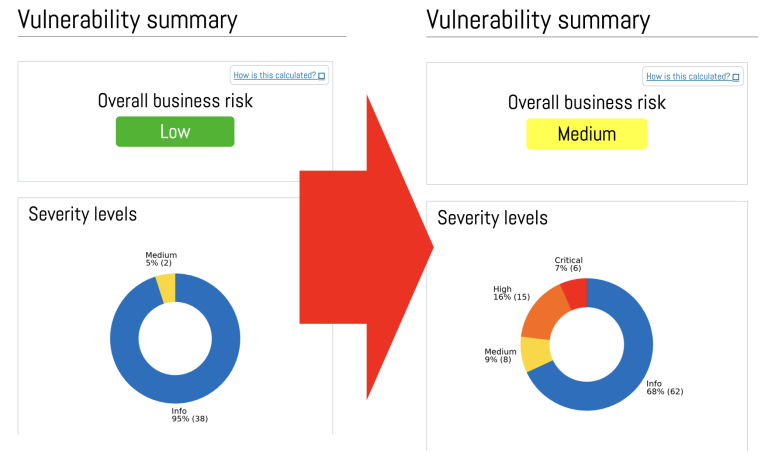
When vulnerabilities are scanned from the perspective of an outside attacker and without actually logging in to the target system(s), only a limited and narrow picture of exposure to threats can be found. For a better picture, it is a good idea to log in with the right kind of credentials.

Today at AlphaSOC we released Network Flight Simulator (flightsim) 2.2.1, which is our free, open source adversary simulation tool. This latest release includes a number of new modules that security teams can use to instantly evaluate detection and response coverage within SIEM and SOAR tools.
To fulfill the training requirements of ISO 27001, the organization must identify what the staff need to learn, train the staff and measure the training’s effectiveness. KnowBe4 is the first and largest next-generation security training and phishing simulation platform. It’s built to be user-friendly and highly intuitive to help busy IT professionals — who have a lot of stuff on their plate already, on an ongoing basis.

All organizations are unique in their security needs and capabilities, and ISO 27001 does not seek to change that fact. The standard guides the adoption of appropriate processes and practices to improve, clarify, and maintain information security as an integral part of day-to-day operations.
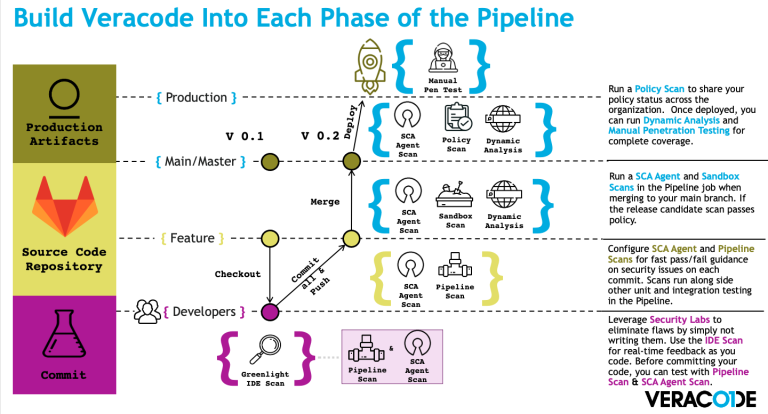
Julian (Veracode) and Thomas (Mint Security) show demos and presentations about running Veracode in CI/CD pipelines.

Do you need independent experts’ assessment of the general security aspects of your application or system? How about a comparable benchmark for the level of your application’s overall security practices?

Do you seek ISO 27001 compliance? Thomas has blogged about starting points for ISO 27001 certification project. This blog unwraps the importance of risk management in pursuit of ISO 27001 certification.

Kun tarkastellaan yrityksen tai organisaation kyberturvallisuustrategiaa, on siihen nykyään myös sisällytettävä yrityksen työntekijät, jotka ovat kyberpuolustuksen ns “inhimillinen osatekijä” (human element). Voidaan varmaan olettaa, että

22.09.2020 We at Mint Security wanted to have a look at… We scanned Koronavilkku – these are our findings 30.06.2020 Developers are, in effect, the
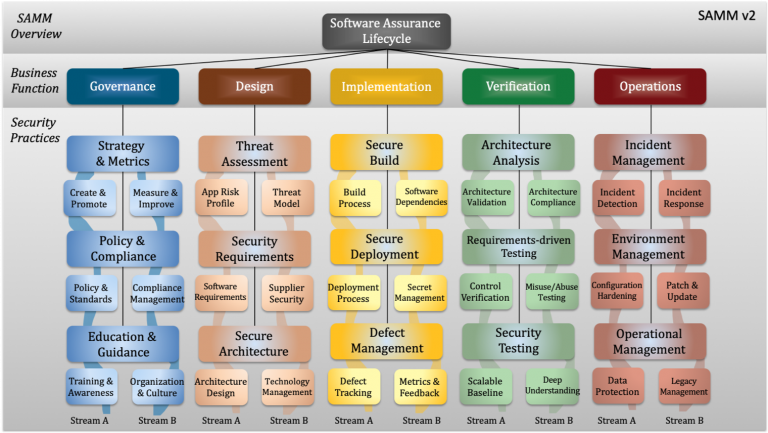
Over the last 10+ years, OWASP SAMM has proven an effective model for improving secure software practices to a wide variety of organizations. Release v2 of SAMM adds automation along with maturity measurements which assess both coverage and quality. Here we look at some the new features and changes compared to the previous version.

We at Mint Security wanted to have a look at the Koronavilkku application and pitch in. The application proved to be of very high quality securitywise. There were no significant security findings.
Recon and red teaming can be done separately, but they also work hand in hand. It may be a good idea for a company to do a thorough recon to understand the adversaries view on the organization – and this not only in the technical sense.
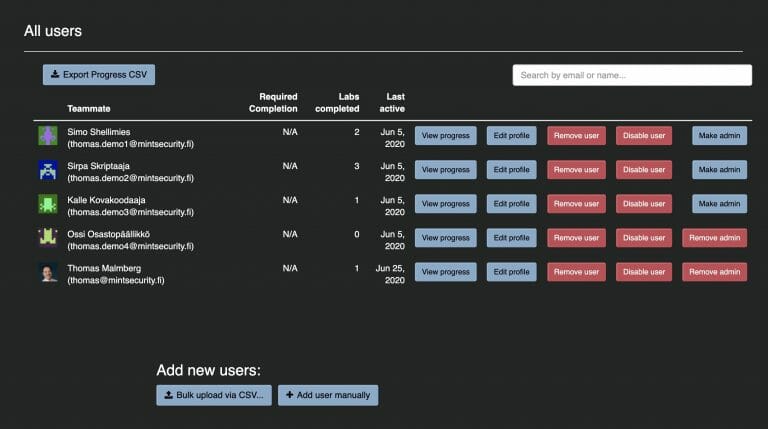
Developers are, in effect, the only people in any organization who can fix vulnerabilities hidden in their applications. Veracode Security Labs helps meet the requirements of security standards while providing a meaningful way for the entire development team to learn more.
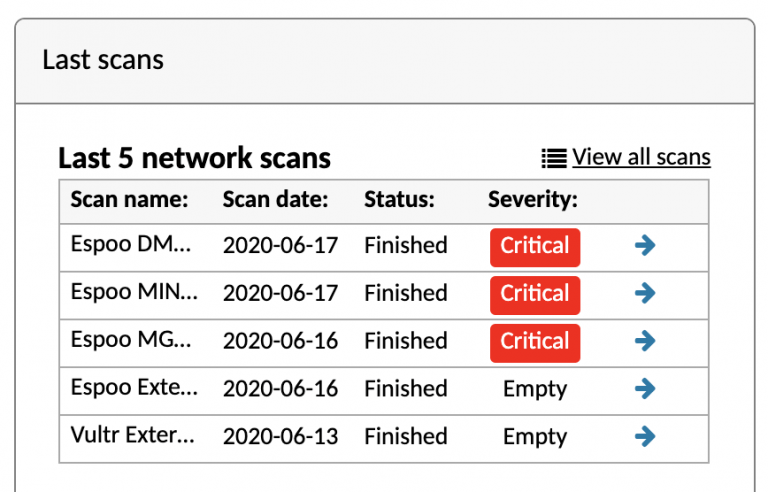
How much common ground is shared between technical vulnerability scanners and the de facto global information security standard? Quite a lot, actually. In this blog post we examine how Holm Security VMP platform meets ISO 27001 requirements for detecting vulnerabilities in an organization’s information systems, assessing the involved risks and taking corrective actions.
Managing a Splunk installation can be a complex task, but with proper tools and processes, it will become a lot more approachable. Recently, a customer wanted to have a Splunk environment that they could install and manage with Ansible. So that is what we created.
Planning for an industry standard compliant information security management system — in brief: carrying out an ISO 27001 project — can break cover from various starting points. Some organizations have already familiarized themselves with the standard, some have even written the first mandatory documents. Yet for many, this article could be the first contact with any form of security work at all.
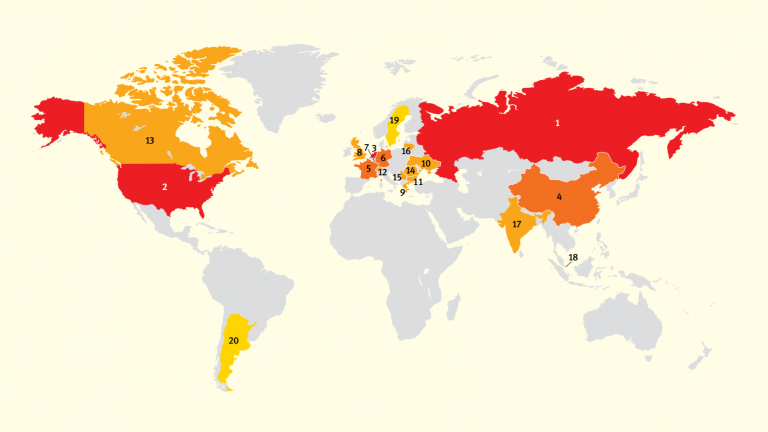
Researchers at Spamhaus Malware Labs identified and blocked 17,602 botnet C&C servers hosted on 1,210 different networks. That is an enormous 71.5% increase from the number of botnet C&Cs seen in 2018. Since 2017, the number of newly detected botnet C&Cs has almost doubled from 9,500 to 17,602.
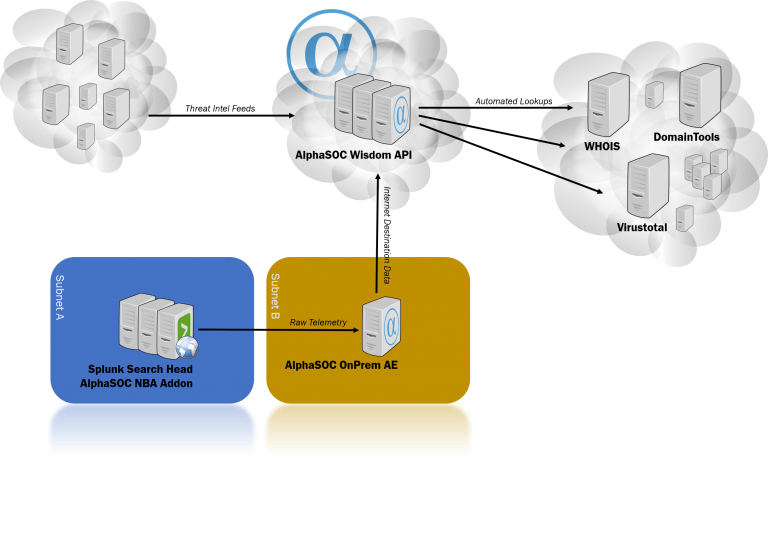
“The cloud!” somebody shouts out loud. “This means my data is sent to the cloud – my precious telemetry data that in the hands of the bad guys could reveal too much about myself!”. This is correct. And for the sake of transparency, let’s have a look at what actually goes on behind the scenes.
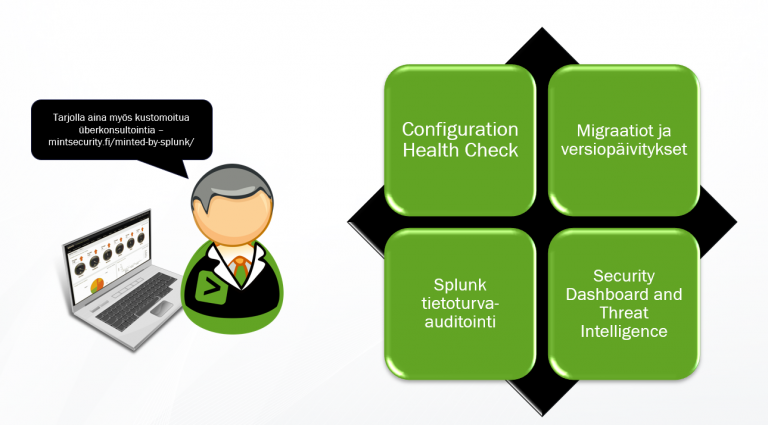
Mint Security tarjoaa Splunkia käyttäville erilaisia lisäarvollisia Splunk konsultointipalveluita jolla saadaan omasta ympäristöstä kaikki irti – turvallisesti.

Through Network Behavior Analytics for Splunk and our native integrations for Demisto and Graylog, we instantly enrich network indicators (FQDNs, URLs, and IP addresses) to provide security teams with hunting material.
This blog post will show you how to integrate Travis CI and Veracode. Travis is a cloud based continuous integration (ci) service, that can be used to automate tests and builds for software projects hosted in GitHub.
Clustered Splunk Enterprise installations are mainly managed by the related management nodes. Indexer Cluster with the Cluster Master and Search Head Cluster with the Search Head Cluster Deployer. Without an additional process of change management, there is no way to easily track down what has been changed, by who and when.
Mint Security has a set of predefined delivery models to choose from. These are based on best practices and experience.
A common tool used to assess the security of a web application is penetration testing. Known also as pentest. Pentest is a “legal” simulated attack that seeks to use an application in a way that could be harmful to either the system, the data in the system, or the people who use the system.
So, you’ve got your Splunk Enterprise up and running and collecting data from some of your systems. A few dashboards have been created too and life is good. But perhaps, there could be more .

Prove your company’s secure software development practices with Veracode Verified. Implementing this program helps you make security part of your competitive advantage, easily defend your AppSec budget, and better integrate security with development.

When Spamhaus Malware Labs observe a 100% increase in the number of domains that are being registered by cybercriminals to host a botnet command & control (C&C) it’s time to stop. Cybercriminals prefer to use a domain name registered exclusively to host a botnet C&C
Mint Security is a Splunk partner and a license reseller. In addition, Mint Security provides a vast range of überconsulting for Splunk. From a single server to clustered multisite setups with integrated SSO and 2FA.

As the use of open source code in development projects continues to grow exponentially, software development teams must take great pains to address open source risk.
Splunk Enterprise is known as a de-facto do-it-all log collector, that in reality is fairly easy to start with, but can be complex to master.

CIRCLean is a independent open source software built on the Raspberry PI. It transfers files from untrusted to trusted USB sticks. CIRClean adds a ‘.DANGEROUS’ filename extension to all suspicious files.
This post is not a technical silver bullet. Nor is it the absolute truth. As a starting point though it is good. It adheres to common sense, is based on risk analysis – and provides good value for the effort.
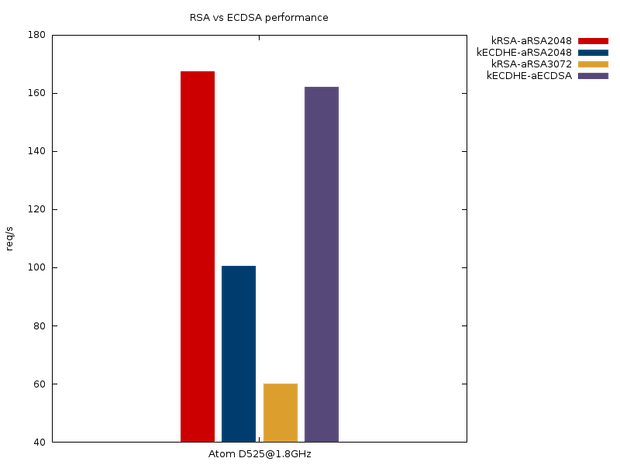
The main points in this post are about the different E’s (elliptic and ephemeral) as well as EC in the key exchange and the certificate signature algorithms.
Please do contact us. We most likely respond faster than you thought,
