How much common ground is shared between technical vulnerability scanners and the de facto global information security standard? Quite a lot, actually. In this blog post we examine how Holm Security VMP platform meets ISO 27001 requirements for detecting vulnerabilities in an organization’s information systems, assessing the involved risks and taking corrective actions.
What Holm Security VMP?
Holm Security Vulnerability Management Platform (VMP) provides a versatile and reliable solution to meet the requirements of the ISO 27001. Suitable targets for inspection include computers, active network devices and other information systems, as well as web applications. In addition to comprehensive scanning features, the platform includes tools to protect users and raise awareness of social engineering, as well as organizing ongoing security work.
What does ISO27001 say about vulnerabilities?
When it comes to managing vulnerabilities, ISO27001 requires three main topics to be considered in the organization:
Scan
Scan
Assess
Assess
Remediate
Remediate
How does Holm Security meet the standard's requirements?
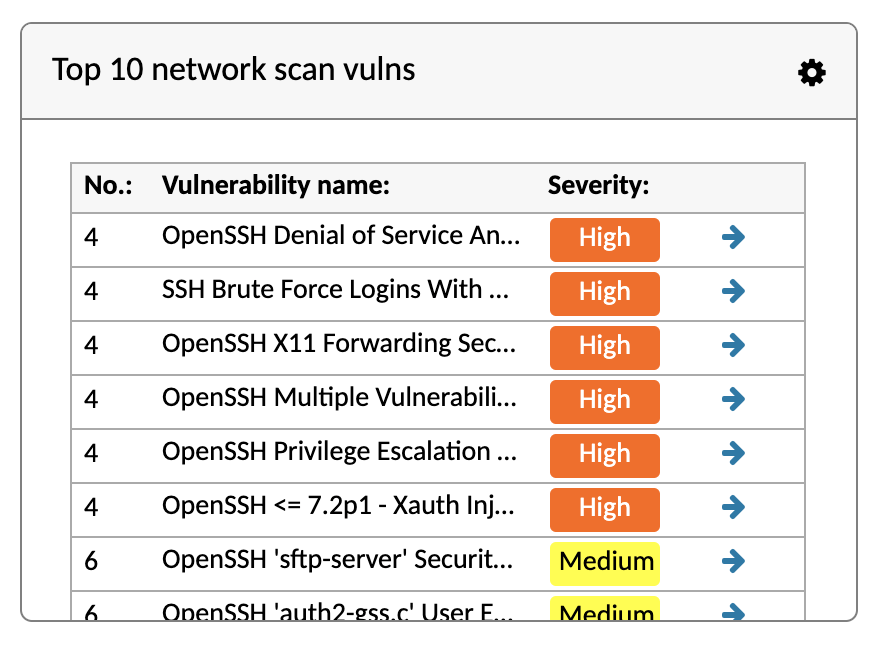
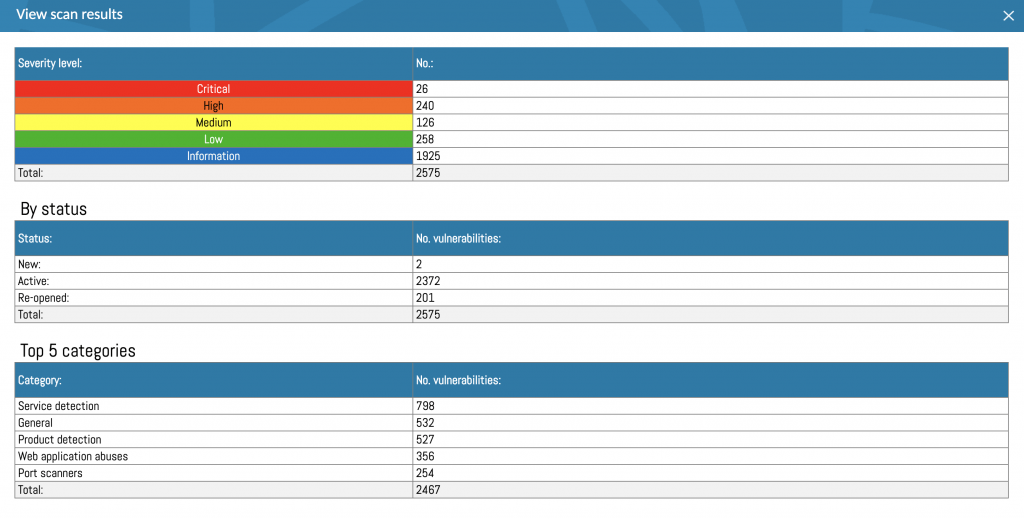
With VMP, it is possible to do both scheduled and on-demand scans. You can even find 0-day vulnerabilities soon enough and still have the time to patch those holes before problems occur. For high-risk systems, you can schedule multiple scans a day if necessary, or enable continuous monitoring to receive alerts immediately when suspicious events are detected.
Not every vulnerability poses the same risk to every organization. In VMP, it’s possible to classify assets based on their business importance and then automatically have the platform determine the risk score for each observed vulnerability.
Once the vulnerabilities have been identified and corresponding risk scores determined, VMP allows you to monitor the remediation progress and monitor allocation of available resources. It is also possible to integrate VMP with Jira.
To demonstrate compliance with the standard, you will also need compliance and trend reports for different audiences such as company management, the board and auditors. Holm Security VMP generates these reports for you, automatically.
Asset inventory
According to ISO 27001, a current and complete inventory of assets is a must-have prerequisite for vulnerability management to be effective. Assets associated with information and information processing facilities should be identified and an inventory of these assets should be drawn up and maintained.
VMP provides a detailed view of assets, which is updated automatically with each scan. You can assign owners and set assets’ business criticality, an up-to-date list of open ports and vulnerability trend charts for each host individually. You might also find systems that should no longer be there in the first place, ports that should be closed or services that are in the wrong place.
Reference sources
You need to know what you’re looking for. ISO 27001 mandates that Information resources that will be used to identify relevant technical vulnerabilities and to maintain awareness about them should be identified for software and other technology (based on the asset inventory). These information resources should be updated based on changes in the inventory or when other new or useful resources are found.
VMP is fully equipped with latest vulnerability data from various sources and constantly updated tests, so you can rest assured that not a single relevant vulnerability goes unnoticed.






