USB memory sticks are a significant daily cyber threat to the business world. They can be dangerous in so many different ways. These easy-to-use and compact storage devices have – for the last 15 years – provided thieves and other malicious actors a simple tool to spread viruses and malware and bypass the layer between secure and insecure networks.
Any device that externally resembles a thumb drive can, in actual fact, be a keyboard in disguise which – when connected to a computer – would immediately start executing malicious commands. Respectively, a USB stick that introduces itself as a network adapter could alter the DNS settings of the operating system, allowing the attacker to eavesdrop and manipulate network traffic. Furthermore, a certain device exists – commonly known as ‘USB killer’ – that sends high-voltage power surges into the port it is connected to, causing severe physical damage to the computer.
An acknowledged threat
Well-informed users are aware of and familiar with the risks associated with USB storage devices. Security instructions often warn employees to not connect unknown and retired thumb drives to their PCs. Instead, people are encouraged to give these devices to IT for a detailed analysis and safe disposal. But what more can IT actually do? This is where a USB sanitizer steps in.
CIRCLean
CIRCLean is a independent open source software built on the Raspberry PI. It transfers files from untrusted to trusted USB sticks. CIRClean adds a ‘.DANGEROUS’ filename extension to all suspicious files. If a file successfully passes all conducted tests without errors, it will be copied to the trusted stick without modifications or renaming. Use of CIRClean does not require a display, nor a network connection. There are no runtime settings for the user to fiddle with and logging on to the system using a keyboard or any other means is not possible.
Installation can be done using a provided disk image, which can be copied to a flash card using dd utility or a similar tool; or alternatively the software can be built and compiled from sources available on Github.
The sanitation process
- connect the trusted device into the top right USB port and the untrusted device into the port directly below that
- Raspberry PI used here as an example is model 3 B+ with four USB ports, CIRClean homepage shows a 2-port model – correct ports can be found by trial and error
- power up the Raspberry PI, and sanitation process will go from start and finish without user interaction
- you can hook up speakers or headphones and enjoy some sweet MIDI tunes while sanitation takes place
- external display can be used to monitor the progress of tests
- as the music stops playing and/or Raspberry PI leds stop flashing, the sanitation process is complete and you can now begin inspecting the files on the trusted USB stick
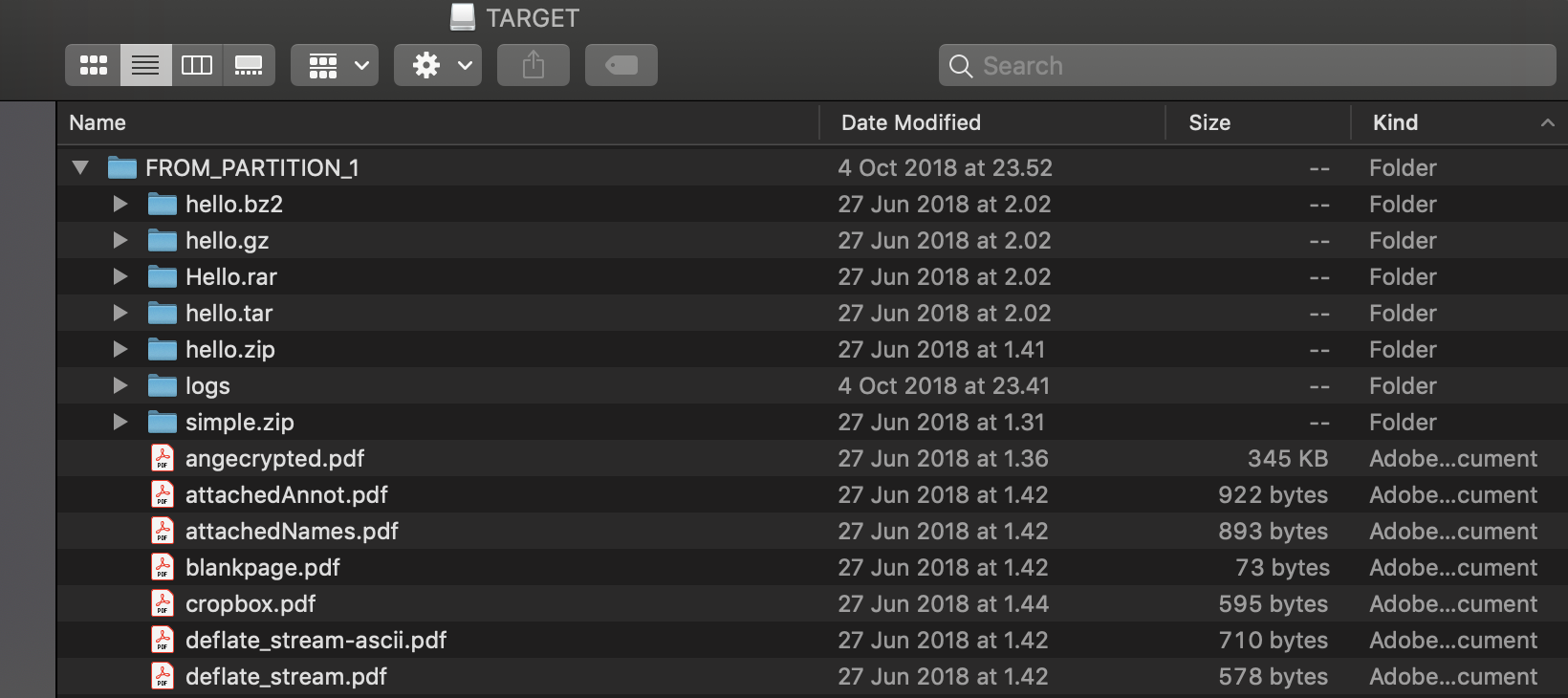
Example list of files produced by CIRCLean..
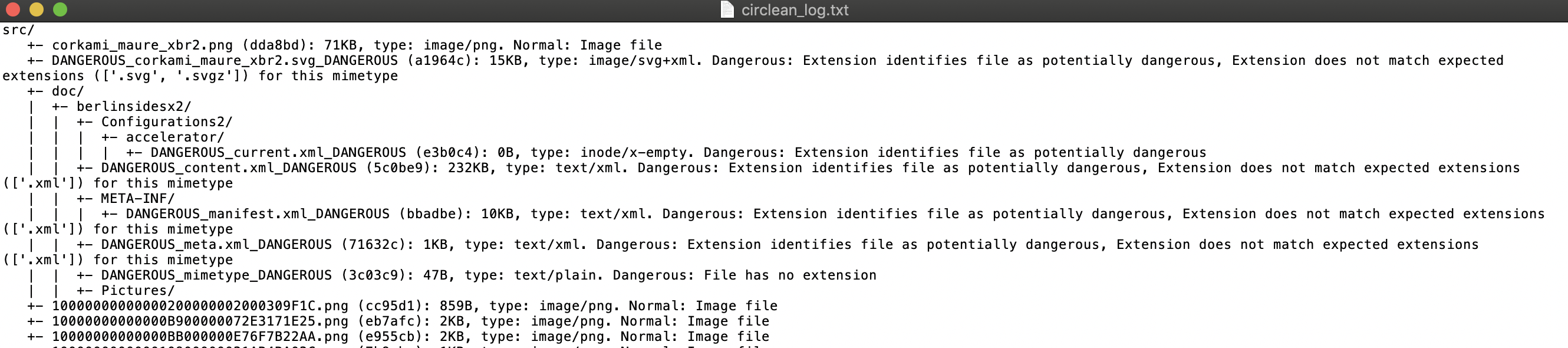
‘Logs’ folder contains detailed information about the tests and test results.
Ease of use and risks
USB sanitation is the right thing to do in a situation where contents of unknown storage devices need to be sorted out. CIRCLean will complete the sanitation process within minutes, in case there are just a few files to be analyzed and they are in common business formats. Therefore it is also suitable for use in customer service situations.
In a worst-case scenario, a malicious thumb drive will break the Raspberry Pi. However, from a financial standpoint, such an event would be significantly less painful than compared to a complete breakdown of a corporate laptop or the damages incurring by rapidly spreading malware in the network.






