Over the last 10+ years, OWASP SAMM has proven an effective model for improving secure software practices to a wide variety of organizations. Release v2 of SAMM adds automation along with maturity measurements which assess both coverage and quality. Here we look at some the new features and changes compared to the previous version.
SAMM and Agile
OWASP SAMM 2.0 is development paradigm agnostic, which is why Agile is not explicitly covered, but rather supported — along with waterfall, iterative and DevOps development.
Agile holds people over process and working software over documentation. Agile wants processes and documentation minimized, where possible. OWASP SAMM can support the Agile way of improving the way work is done, by learning on the go.
-
Activities
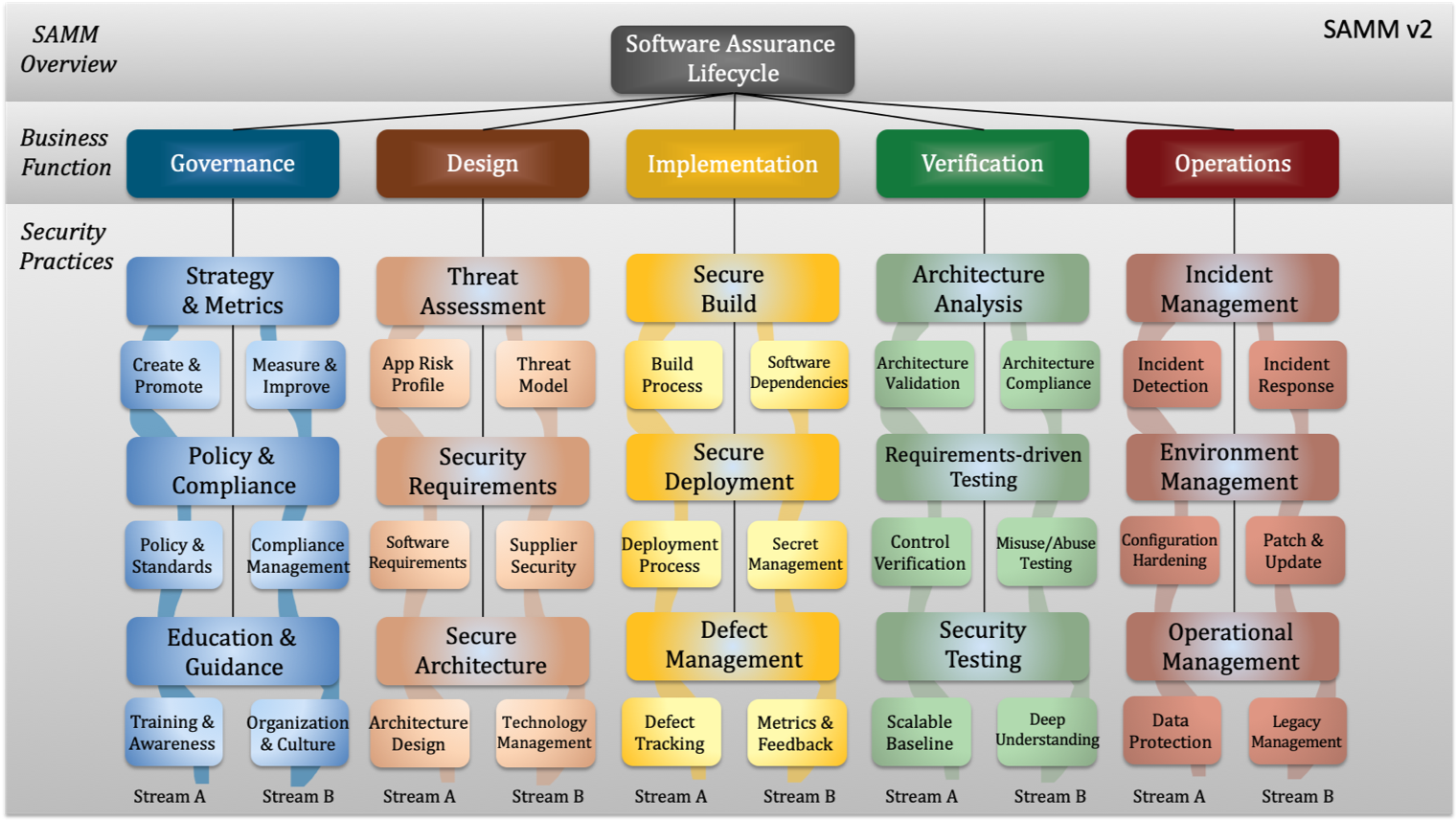
Activities are now presented in logical flows throughout each of the now 15 security practices, divided into two streams, which aligns and links the activities in the practice over the different maturity levels
-
Streams
Each stream has an objective that can be reached in increasing levels of maturity. This way, there are no “orphan” activities that seem only relevant on a single maturity level (for instance, code signing in the previous model)
-
Maturity levels
The model now supports maturity measurements both from a coverage and a quality perspective. There are new quality criteria for all the SAMM activities, and an updated scoring model to help SAMM assessors and organizations with their software assurance
Structure and organization
Key organizational changes in OWASP SAMM release 2.0 include.
ADDED
New Operational Management Practice
ADDED
New Business function – Implementation
MODIFIED
ELIMINATED
Implementation represents a number of core activities in the build and deploy domains of an organization and also includes a new security practice that deals with Defect Management. Construction was renamed to Design and Verification went through a redesign. Other core Business Functions, Governance and Operations, remain as they were.
Structure and organization
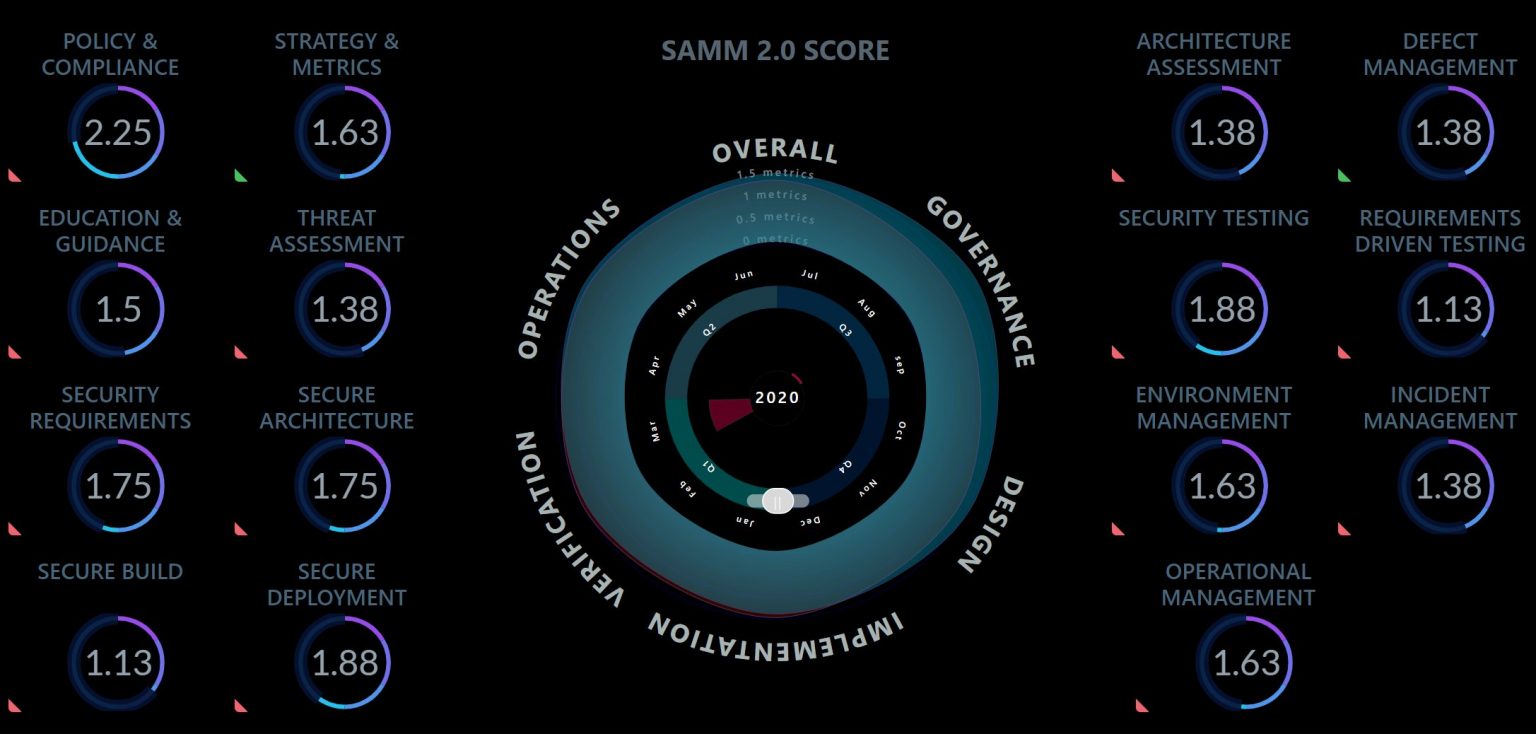
The app
SAMM is fueled by community additions. One of them is the all new dashboard. It looks fancy but may prove a bit tricky to setup properly. We did, and this is how it looks.
How does SAMM and BSIMM compare?
Where OWASP SAMM is a prescriptive model, BSIMM is descriptive. BSIMM contains a set of activities and their respectful activity levels and the overall goal is to observe and report these observations.
SAMM measures maturity against a prescriptive set of practices and BSIMM the maturity of your organisation relative to its peers.
The most important links
Have a look at these important resources scattered around the SAMM household. The SAMM website has a lot of information, but maybe not always in the most logical structure. These links will get you started.
- https://owaspsamm.org/guidance/agile/
- This is where SAMM leaped into 2020 – agile development
- https://owaspsamm.org/mapping-versions/
- This assists in mapping to previous versions
- https://owaspsamm.org/release-notes-v2/
- This contains the major changes in a nutshell
- https://github.com/OWASP/samm/blob/master/Supporting%20Resources/v2.0/toolbox/SAMM_Assessment_Toolbox_v2.0.xlsx
- This is The Tool – start actually using SAMM
- https://github.com/OWASP/samm/tree/master/Supporting%20Resources/app
- This is the ”app” – the dashboard. The installation is not very enterprisey or robust – don’t hesitate to ask for ideas on how to install this.






