- Network Scanning
- Web App Scanning
- Fraud Risk Assessment
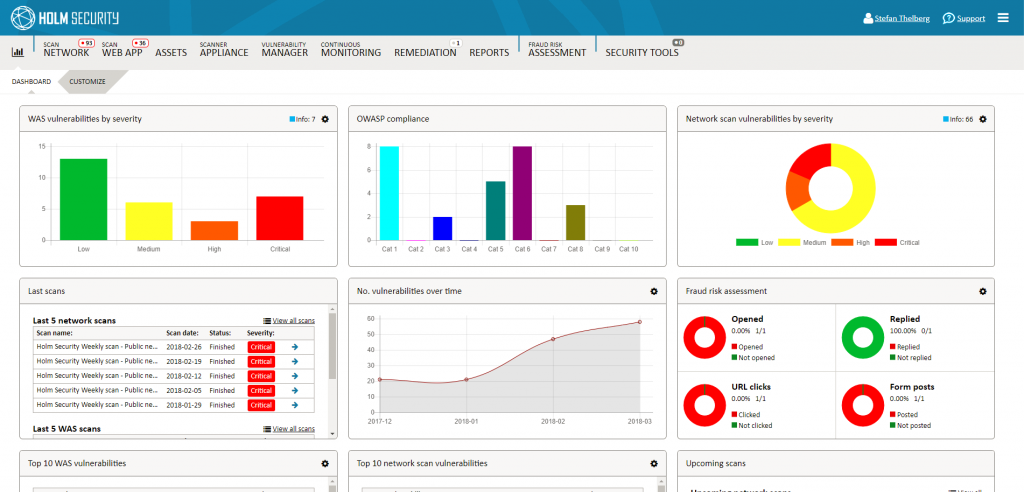
 Holm Security Vulnerability Management Platform – VMP
Holm Security Vulnerability Management Platform – VMP
Suojaa organisaatiosi havaitsemalla haavoittuvuudet ennen kuin ilkeämielinen taho ehtii tunkeutua verkkoon. Holm Security VMP -alusta sisältää verkkojen ja verkkosivustojen haavoittuvuuksien arvioinnin ja riskianalyysit sosiaalista manipuloinnin varalta sekä useita työkaluja, jotka helpottavat jatkuvaa turvallisuustyötä.
Holmin alusta auttaa organisaatiota näkemään, miten turvallinen IT-ympäristö ja sen käyttäjät ovat ulkoisia uhkia, kuten hakkereita, vastaan – sekä omassa tai ulkoistetussa ympäristössä. Palvelua voi hallita helposti ja tehokkaasti verkkopohjaisen Security Center -ohjauspaneelin avulla. Holm Security VMP -alustaa käytetään moderneista ja turvallisista palvelinkeskuksista.
 Tehokkain tapa ymmärtää tietoturvaa
Tehokkain tapa ymmärtää tietoturvaa
Verkkojen ja järjestelmien turvallisuudesta voidaan huolehtia Holm Securityn verkkoskannauksen avulla. Palvelu tarkistaa kohteet yli 60 000 haavoittuvuuden varalta. Riippumatta siitä, hallitaanko kaikkia IT-järjestelmiä itse vai käytetäänkö ulkoistettua verkkoa, Holm Securityn verkkoskannaus on tehokkain tapa selvittää kuinka turvallinen verkko on ulkoisia uhkia vastaan. Lisäksi se on tehokas tapa korjata haavoittuvuudet ja näin lisätä tietoturvaaa hyvin pienellä vaivalla. Palvelu tarjoaa myös valikoiman tukitoimintoja GDPR- ja NIS -direktiivien vaatimusten mukaiseen toimintaan.
Verkon ja järjestelmien automaatisoitu ja jatkuva skannaus
Holm Security -verkkoskannaus tarkistaa verkot ja järjestelmät automaattisesti ja jatkuvasti yhä lisääntyvien haavoittuvuuksien varalta. Verkkoskannaus havaitsee vanhoihin ohjelmistoihin, riskialttiisiin palveluihin ja toimintoihin, virheellisesti määritettyihin järjestelmiin, heikkoihin salasanoihin jne. liittyviä haavoittuvuuksia. Lisäksi palvelu kartoittaa verkon automaattisesti, jotta saadaan selkeä yleiskuva kaikista järjestelmistä – riippumatta missä järjestelmät sijaitsevat, tai hallitsetko kaikkea itse vai onko IT-ympäristö ulkoistettu kokonaan tai osittain.
Käyttämällä kattavia tietoja, älykkäitä ja tehokkaita työkaluja sekä tukea ja asiantuntija-apua, oma organisatio tai IT-kumppani voi priorisoida ja korjata havaitut haavoittuvuudet tehokkaasti, ennen kuin kukaan ehtii käyttää niitä hyväkseen.
Verkkojen ja järjestelmien suunnitellun tarkistuksen ohella skannauksen voi käynnistää milloin tahansa, esimerkiksi muutosten ja käyttöönoton yhteydessä.
Kattaa koko IT-ympäristön
Pilvesta tarjottava skanneri tarkistaa Internetin kautta käytettävät julkiset verkot ja järjestelmät. Sisäverkkojen skannaukset tehdään asentamalla yksi tai useampi virtuaalikone paikallisiin ympäristöihisi palomuurin taakse. Kaikki skannauksista kerätty data esitetään pilvipohjaisen hallintapaneelissa (Security Center).
Haavoittuvuuksien hallinta
Haavoittuvuuksien hallinta (Vulnerability Management) on tehokas työkalu, jolla haavoittuvuudet voi käsitellä tehokkaasta lukumäärästä riippumatta. Haavoittuvuudet voi lajitella, ryhmitellä, sivuuttaa ja priorisoida haavoittuvuudet juuri sillä tavalla, joka toimii parhaiten omassa ympäristössäsi. Työkalu tarjoaa useita erilaisita toimintoja, joiden avulla voidaan tehostaa yhteistyötä organisaation sisällä ja ulkopuolisten kumppaneiden, kuten esim. IT-ulkoistuskumppanin kanssa.
Jatkuva tarkkailu
Jatkuvan valvonnan (Continuous Monitoring) avulla voidaan nopeasti ja vaivatta määritellä muutosten seurannan sekä tarvittavat ilmoitukset ja hälytykset. Työkalua kätettäessä ei ole enää välttämätöntä työskennellä Security Centerissä. Toiminto ilmoittaa, kun uusia haavoittuvuuksia havaitaan, tai kun muutoksia tehdään tai kun haavoittuvuudet on korjattu. Toiminnossa voidaan määrittää esimerkiksi järjestelmät, jotka käsittelevät henkilötietoja GDPR-vaatimustenmukaisuuden takaamiseksi, tai sinne voidaan määritellä erityinen verkko, jolla saadaan tietoja avatuista tai suljetuista porteista.
Korjausprosessi
Palvelu sisältää kattavan välineen korjausprosessin hallintaan. Työnkulku on suurelta osin automatisoitu. Tehtävät määritellään ja osoitettaan työjonoon asetettujen sääntöjen mukaan. Työkalu on mahdollista integroida ulkoisiin korjausjärjestelmiin.
Raportit
Palvelussa on saatavilla useita valmiita raporttimalleja, ja voit luoda myös omia raportteja, jotka on suunniteltu eri kohderyhmille kuten teknikoille ja asiantuntijoille tai yritysjohdolle, toimitusjohtajalle ja hallitukselle. Raportit jaetaan salatussa muodossa, esimerkiksi IT-kumppanille tai järjestelmätoimittajalle. Voit luoda raportteja automatisoidusti halutun aikataulun mukaan tai oman tarpeen mukaan milloin tahansa.
Toiminnot GDPR- ja NIS-direktiivien noudattamiseen
Palvelu tarjoaa joukon GDPR- ja NIS -direktiivien vaatimustenmukaisuuden tukitoimintoja, joilla voidaan muun muassa tarkistaa henkilötietoja sisältävät tietojärjestelmät seurantaa varten ja luoda automaattisesti raportteja rekisterinpitäjälle.
 Web-sovellukset – yleinen hyökkäyskohde
Web-sovellukset – yleinen hyökkäyskohde
Useat riippumattomat asiantuntijat arvioivat, että noin 70% kaikista verkkosovelluksista (verkkosivustoista) on mahdollista hakkeroida. Tutkimusyhtiö Gartnerin mukaan 75% hyökkäyksistä tapahtuu sovelluskerroksessa, mikä tekee verkkosovelluksista IT-ympätistön haavoittuvimman kerroksen. Verkkosovellukset ovat usein avoinna koko internetille, mikä lisää huomattavasti haavoittuvuuksien hyväksikäytön riskiä.
Verkkosovellusten automatisoitu ja jatkuva skannaus
Holm Security VMP skannaa automaattisesti ja jatkuvasti verkkosovellukset ja REST API -sovellusrajapinnat yhä lisääntyvien haavoittuvuuksien varatalta. Verkkosovellusten skannauksella havaitaan vialliseen koodiin, virheellisesti määritettyihin järjestelmiin, heikkoihin salasanoihin sekä altistuneisiin järjestelmiin ja henkilötietoihin liittyviä haavoittuvuuksia.
Käyttämällä kattavia tietoja, älykkäitä ja tehokkaita työkaluja sekä tukea ja asiantuntija-apua, oma organisatio tai IT-kumppani voi priorisoida ja korjata havaitut haavoittuvuudet tehokkaasti, ennen kuin kukaan ehtii käyttää niitä hyväkseen.
Verkkosovellusten suunnitellun tarkistuksen ohella skannauksen voi käynnistää milloin tahansa, esimerkiksi muutosten ja käyttöönoton yhteydessä.
Kattaa koko IT-ympäristön
Pilvesta tarjottava skanneri tarkistaa Internetin kautta käytettävät julkiset verkot ja järjestelmät. Sisäverkkojen skannaukset tehdään asentamalla yksi tai useampi virtuaalikone paikallisiin ympäristöihisi palomuurin taakse. Kaikki skannauksista kerätty data esitetään pilvipohjaisen hallintapaneelissa (Security Center).
Haavoittuvuuksien hallinta
Haavoittuvuuksien hallinta (Vulnerability Management) on tehokas työkalu, jolla haavoittuvuudet voi käsitellä tehokkaasta lukumäärästä riippumatta. Haavoittuvuudet voi lajitella, ryhmitellä, sivuuttaa ja priorisoida haavoittuvuudet juuri sillä tavalla, joka toimii parhaiten omassa ympäristössäsi. Työkalu tarjoaa useita erilaisita toimintoja, joiden avulla voidaan tehostaa yhteistyötä organisaation sisällä ja ulkopuolisten kumppaneiden, kuten esim. IT-ulkoistuskumppanin kanssa.
Jatkuva tarkkailu
Jatkuvan valvonnan (Continuous Monitoring) avulla voidaan nopeasti ja vaivatta määritellä muutosten seurannan sekä tarvittavat ilmoitukset ja hälytykset. Työkalua kätettäessä ei ole enää välttämätöntä työskennellä Security Centerissä. Toiminto ilmoittaa, kun uusia haavoittuvuuksia havaitaan, tai kun muutoksia tehdään tai kun haavoittuvuudet on korjattu. Toiminnossa voidaan määrittää esimerkiksi järjestelmät, jotka käsittelevät henkilötietoja GDPR-vaatimustenmukaisuuden takaamiseksi, tai sinne voidaan määritellä erityinen verkko, jolla saadaan tietoja avatuista tai suljetuista porteista.
Korjausprosessi
Palvelu sisältää kattavan välineen korjausprosessin hallintaan. Työnkulku on suurelta osin automatisoitu. Tehtävät määritellään ja osoitettaan työjonoon asetettujen sääntöjen mukaan. Työkalu on mahdollista integroida ulkoisiin korjausjärjestelmiin.
Raportit
Palvelussa on saatavilla useita valmiita raporttimalleja, ja voit luoda myös omia raportteja, jotka on suunniteltu eri kohderyhmille kuten teknikoille ja asiantuntijoille tai yritysjohdolle, toimitusjohtajalle ja hallitukselle. Raportit jaetaan salatussa muodossa, esimerkiksi IT-kumppanille tai järjestelmätoimittajalle. Voit luoda raportteja automatisoidusti halutun aikataulun mukaan tai oman tarpeen mukaan milloin tahansa.
Toiminnot GDPR- ja NIS-direktiivien noudattamiseen
Palvelu tarjoaa joukon GDPR- ja NIS -direktiivien vaatimustenmukaisuuden tukitoimintoja, joilla voidaan muun muassa tarkistaa henkilötietoja sisältävät tietojärjestelmät seurantaa varten ja luoda automaattisesti raportteja rekisterinpitäjälle.
 Käyttäjien testaus
Käyttäjien testaus
Arvioiden mukaan organisaation suurin tietoturvariski ei ole organisaation IT-ympäristö, vaan sen käyttäjät. Järjestelmiä ja tietokoneita voidaan suojata, arvioida ja valvoa niiden turvallisuuden varmistamiseksi, mutta kuinka turvallisia ovat käyttäjät ja kuinka testata heitä? Alle prosentti kaikista Ruotsin yrityksistä tai organisaatioista testaa käyttäjiensä toimintaa tietoturvahyökkäysten varalta, joten ne eivät tiedä mitä tapahtuu, kun henkilöstö joutuu alttiiksi esimerkiksi tietojenkalastelulle, kohdennetulle verkkourkinnalle tai kiristysohjelmien hyökkäyksille.
Sosiaalisen manipuloinin simulointi – phishing-testaus
Holm Security VMP sisältää innovatiivisen ja tehokkaan työkalun, jolla lisätään yritysten ja muiden organisaatioiden ns. sosiaalisesen manipuloinnin vastustuskykyä. Palvelun avulla simuloidaan sähköpostin kautta tapahtuvia hyökkäyksiä. Tulosten perusteella voidaan tarjota käyttäjälle räätälöityä koulutusta. Simuloinnilla saadaan myös arvokkaita tilastoja, joiden pohjata voi ryhtyä jatkotoimiin.
Arviointi on täysin riskitön käyttäjille tai tietojärjestelmille. Simuloinnissa käytetään sähköpostiviestejä ja verkkosivuja. Palvelu sisältää erilaisia malleja, joita voi helposti muokata tai luoda omia sähköpostiviestejä ja verkkosivuja. Tällä tavoin voi toteuttaa eri tasoisia sosiaalisen manipuloinnin hyökkäyksiä ja ns. kohdennettuja verkkourkintaa, jonka kohteena on koko organisaatio tai tietty käyttäjäryhmä.
GDPR-vaatimustenmukaisuus
Kuinka alttiita käyttäjät ovat vuotamaan henkilötietoja? Huijausriskien arviointitoiminnon (Fraud Risk Assessment) avulla voidaan mitata, kuinka alttiita käyttäjät ovat paljastamaan erityyppisiä henkilötietoja – tämä on tärkeä tieto GDPR:n aatimusten noudattamisen kannalta.
Automaatisoitu koulutus
Jokaisen käyttäjälle voidaan räätälöidä automaattisesti koulutus simuloinnissa havaitun käyttäytymisen perusteella. Koulutuksen tiedot antavat paljon hyötyö käyttäjälle. Tiedot perustuvat valmiisiin malleihin tekstin ja kuvituksen muodossa. Lähettäjää ja malleja voidaan vaihtaa vapaasti, ja on mahdollista viitata yrityksen omaan koulutusmateriaaliin. Muutamalla näppäyksellä automaatio auttaa saamaan arvokkaita tilastoja, mutta myös opettamaan käyttäjiä automaattisesti – yksinkertaista ja erittäin tehokasta.
Tilastot
Arvioinnin tulokset koostuvat tilastoista avoimista sähköposteista, klikkauksista, vastauksista sähköpostiin ja lähetetyistä lomakkeista. Tilastoja ei voi yhdistää käyttäjiin ja ne ovat täysin nimettömiä. Eri aikoina tehtyjen arviointien tuloksia voi vertailla keskenään ja näin arvioida ovatko arviointien välillä tehty toimenpiteet tuottaneet toivottuja vaikutuksia.
Sisäänrakennettu yksityisyyden suoja
Tämä palvelu perustuu sisäänrakennetun yksityisyyden suojan periaatteeseen, mikä tarkoittaa, että käyttäjän henkilökohtaista koskemattomuutta ei koskaan vaaranneta. Kaikki arviointiin osallistuvat käyttäjät ovat nimettömiä, eikä arkaluonteisia tietoja tallenneta.